BitViraj Technologies - Your Gateway to
Tomorrow's Innovations

Decoding Crypto Crime: A Comprehensive Guide for Law Enforcement
Cryptocurrencies have revolutionized finance, offering decentralization, anonymity, and fast cross-border transactions. However, these same features make them attractive to criminals. Law enforcement agencies worldwide face growing challenges in tracking and prosecuting crypto-related crimes. This guide provides a detailed overview of common crypto crimes, real-world incidents, and best practices for investigations.
By Bitviraj Technology
May 11, 2026
Decoding Crypto Crime
A Comprehensive Guide for Law Enforcement
Decoding Crypto Crime: A Comprehensive Guide for Law Enforcement
Understanding Cryptocurrency-Related Crimes
Crypto crimes range from fraud and scams to extortion and money laundering. Below are some of the most prevalent types.
Cryptocurrency Investment Schemes (Ponzi & Pyramid)
Fraudsters lure victims with promises of high returns on crypto investments. These schemes often collapse when new investors stop joining.
Real-World Incident: BitConnect (2017-2018)
BitConnect promised daily returns via a "trading bot." It was a Ponzi scheme paying old investors with new deposits. Outcome: collapsed in 2018, losses exceeding $3.45 billion.
Technical Details:
- Used multi-level marketing (MLM) structure, rewarding recruitment.
- Funds funneled through mixers to obscure trails.
Investigation Tips:
- Obtain wallet addresses from victims.
- Track on-chain transactions using blockchain explorers (Etherscan, Blockchain.com).
- Look for large, sudden withdrawals to centralized exchanges.
Extortion & Sextortion
Criminals threaten victims (often with fake compromising material) and demand cryptocurrency payments.
Real-World Incident: The "Sextortion" Email Scam (2020-2023)
Victims received emails claiming hackers had recorded them via webcam, demanding Bitcoin to avoid leaked footage. Outcome: thousands paid out of fear despite being a bluff.
Investigation Tips:
- Check Bitcoin addresses in extortion emails.
- Use Chainalysis or CipherTrace to track fund movements.
“Rug Pull” Scams (DeFi Exit Scams)
Developers abandon a project after raising funds, leaving investors with worthless tokens.
Real-World Incident: AnubisDAO (2021)
Raised ~$60M in ETH, then developers drained liquidity overnight.
Technical Details:
- Smart contract had hidden admin privileges allowing fund withdrawal.
- Funds swapped for ETH and laundered via Tornado Cash.
Investigation Tips:
- Analyze smart contract code for backdoors.
- Monitor liquidity removal on DEXs like Uniswap.
Phishing Scams
Fraudsters impersonate legitimate platforms to steal private keys or login credentials.
Real-World Incident: OpenSea Phishing Attack (2022)
Users received fake emails prompting them to sign a malicious EIP-712 transaction, granting attackers access to NFTs. Losses: over $1.7M in stolen NFTs.
Investigation Tips:
- Check sender addresses in phishing emails.
- Use Etherscan’s Token Approval Checker to revoke malicious permissions.
Man-in-the-Middle (MITM) Attacks
Hackers intercept transactions by compromising Wi-Fi or DNS settings.
Real-World Incident: Ledger Wallet MITM Attack (2020)
Hackers altered DNS records to redirect users to a fake Ledger Live site. Losses: over $1M in stolen crypto.
Investigation Tips:
- Verify SSL certificates of crypto-related sites.
- Educate victims on hardware wallet security.
Fake Cryptocurrency Exchange Websites
Scammers clone legitimate exchange sites to steal login details.
Real-World Incident: Binance Phishing Scam (2023)
Fake Binance sites offered "double your deposit" scams. Losses estimated $5M+ stolen.
Investigation Tips:
- Use WHOIS lookup to track domain registrations.
- Report fake sites to registrars & hosting providers.
Secondary Scams (Recovery Scams)
After a victim is scammed, fraudsters pose as "recovery agents" offering to retrieve lost funds—for a fee.
Real-World Incident: "Crypto Recovery" Twitter Scams (2022-2023)
Scammers impersonated blockchain analysts, demanding upfront payments, sometimes using deepfake videos.
Investigation Tips:
- Warn victims about recovery scams.
- Monitor Twitter & Telegram for impersonation accounts.
Best Practices for Law Enforcement
Key Evidence to Collect:
- Wallet addresses (victim’s and scammer’s).
- Transaction hashes (from blockchain explorers).
- Screenshots of phishing emails/fake websites.
- Smart contract addresses (for DeFi scams).
Tools for Investigations:
- Blockchain Analysis: Chainalysis, Elliptic, TRM Labs.
- Smart Contract Audits: CertiK, SlowMist.
- Exchange Cooperation: Request KYC data from centralized exchanges.
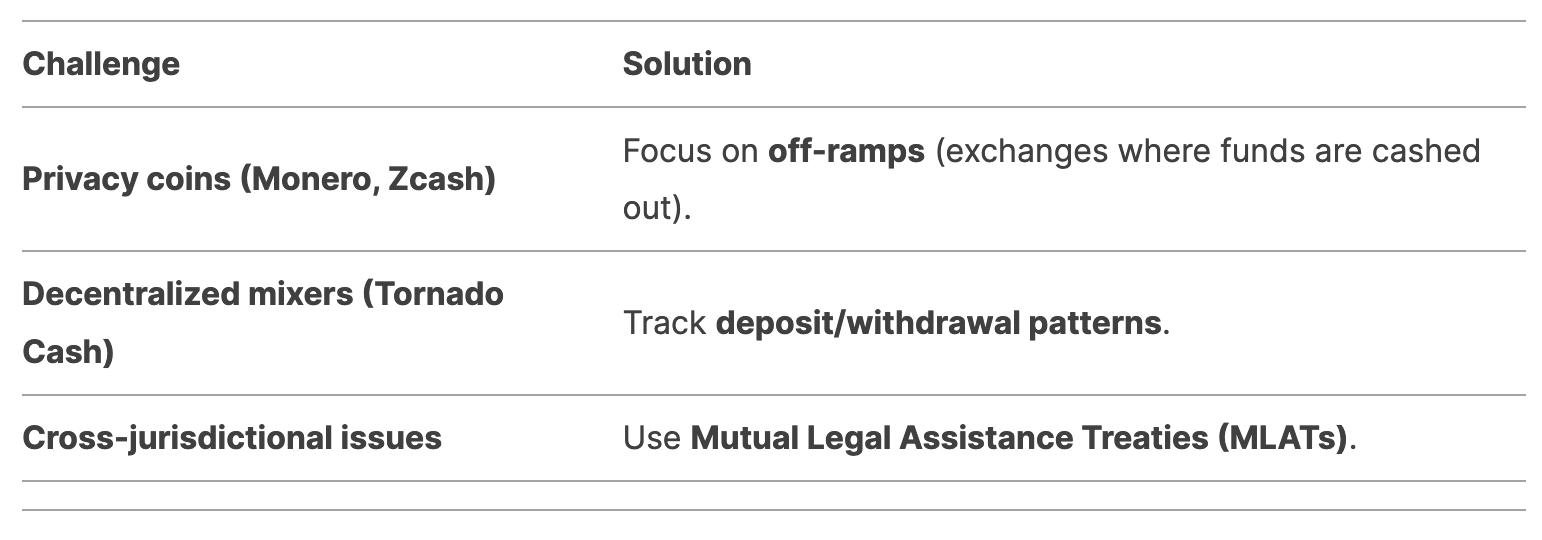
Challenges & Solutions
Conclusion
Cryptocurrency-related crimes are evolving, but law enforcement can stay ahead by leveraging blockchain forensics, international cooperation, and victim education. By following structured investigation protocols, agencies can disrupt criminal networks and recover stolen assets.
Stay vigilant, collaborate globally, and use the right tools – crypto crime can be decoded.
Case Studies
Empowering Digital
Evolution
Blogs
Empowering Digital
Evolution
BitViraj Technologies - Your Gateway to
Tomorrow's Innovations
Embark on a DigitalJourney


The next-generation digital technology company Bitviraj has the potential to empower and reinvent business in the current fast-paced market.
Our Service
- Website Development
- Application Development
- Blockchain Development
- Gaming and Metaverse