BitViraj Technologies - Your Gateway to
Tomorrow's Innovations

The Post-Quantum Migration of Blockchain: An Existential Threat with No Perfect Solutions
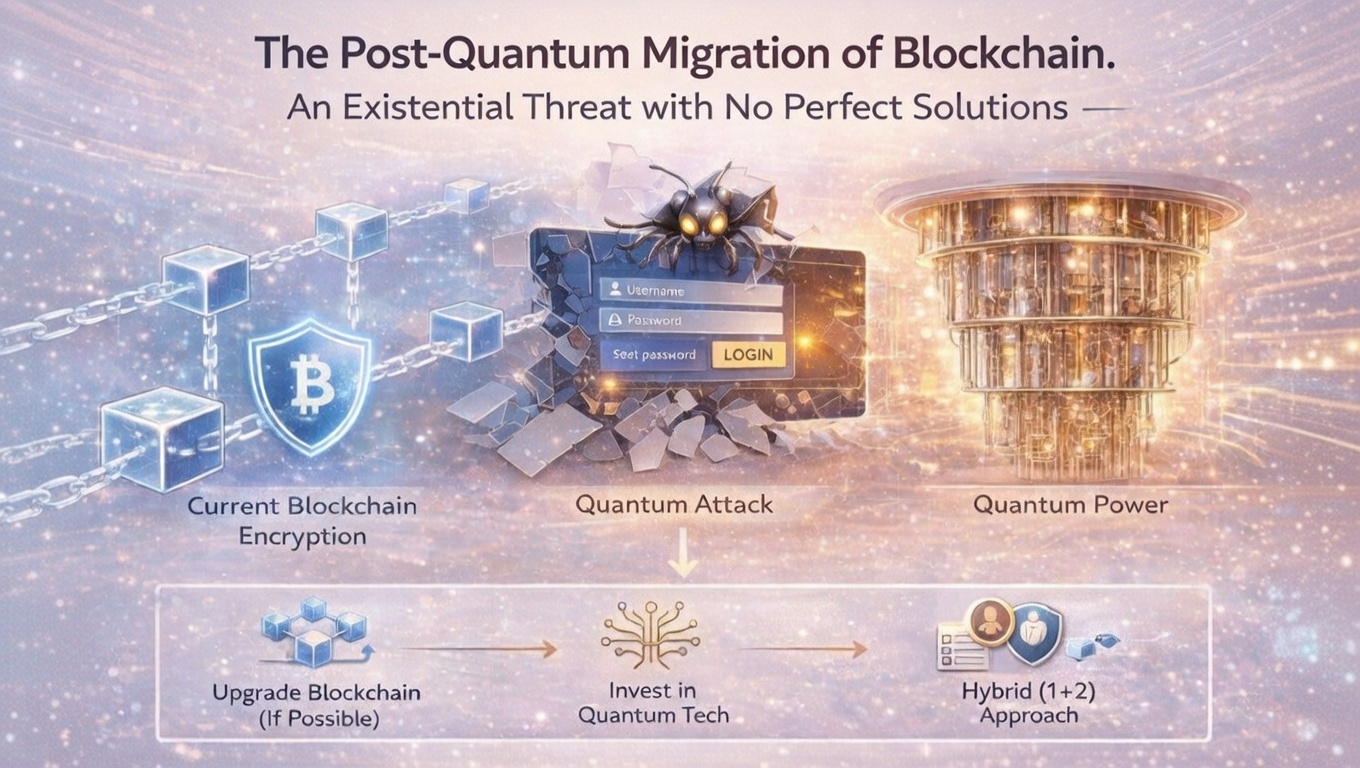
The blockchain ecosystem faces its most formidable security challenge since inception: the emergence of cryptographically relevant quantum computers (CRQCs) capable of breaking the elliptic curve cryptography underpinning virtually every blockchain network.
By Bitviraj Technology
The Post-Quantum Migration of Blockchain
An Existential Threat with No Perfect Solutions
The Post-Quantum Migration of Blockchain: An Existential Threat with No Perfect Solutions
Executive Summary
The blockchain ecosystem faces its most formidable security challenge since inception: the emergence of cryptographically relevant quantum computers (CRQCs) capable of breaking the elliptic curve cryptography underpinning virtually every blockchain network. This comprehensive analysis synthesizes current research, technical specifications, and implementation strategies to reveal a stark reality: the migration to post-quantum cryptography (PQC) represents a defensive downgrade with catastrophic performance implications, occurring against a rapidly closing timeline window.
Critical findings include:
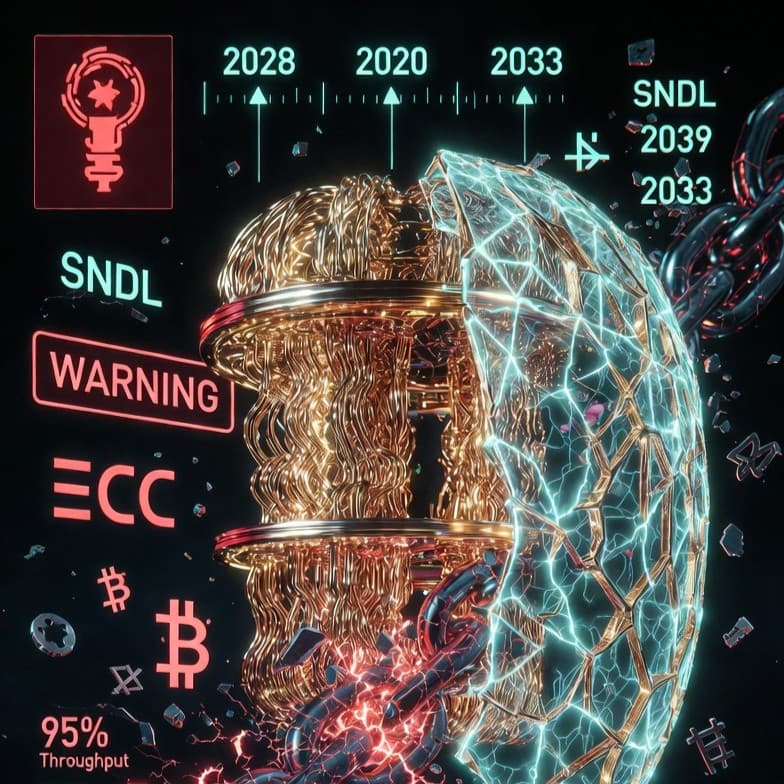
The 10–15 year realistic migration requirement for decentralized networks directly conflicts with the 2028–2033 projected arrival of fault-tolerant quantum computers capable of breaking Bitcoin's secp256k1 curve.
Bitcoin's 1MB blocks would collapse from ~7,600 transactions with ECDSA to ~400 with ML-DSA-65 (Dilithium), representing a 95% throughput reduction that fundamentally challenges blockchain utility.
Unlike beneficial upgrades, PQC migration imposes immediate severe costs with no tangible short-term benefits, creating unprecedented consensus challenges for decentralized systems.
Approximately 20–50% of Bitcoin ~4 million BTC already exists in addresses with exposed public keys, creating a $650+ billion vulnerability window that closes when quantum computers arrive, not when migration begins.
Introduction: The Quantum Threat Landscape
The Quantum Computing Threat Timeline
Quantum computers leveraging Shor's algorithm threaten the fundamental security assumptions of blockchain technology. Unlike classical threats that can be patched reactively, the quantum threat operates on a predictable timeline with permanent consequences for data recorded today.
Critical Quantum Computing Milestones:
2023: IBM's 1,121-qubit Condor processor demonstrated scaling capabilities
2024: Google's Willow chip achieved below-threshold quantum error correction — a critical breakthrough for fault tolerance
2025 Projections: Systems approaching 1,500–2,000 physical qubits with improved error rates
2029 Roadmap: IBM projects 4,000+ qubit systems with early error correction capabilities
2033 Forecast: 100,000+ logical qubit systems potentially capable of breaking RSA-2048 and secp256k1
The threshold for breaking Bitcoin's secp256k1 curve remains debated but falls within 523–2,500 logical qubits. Current systems achieve ~100 logical qubits with error correction, placing the critical threshold within 4–10 years depending on error correction efficiency and algorithmic optimizations.
The Store Now, Decrypt Later (SNDL) Paradox
Blockchain systems face unique SNDL vulnerabilities due to their immutable, public nature:
Bitcoin Exposure Analysis:
P2PK Outputs: Early Bitcoin blocks including Satoshi's approximately 1 million BTC used Pay-to-Public-Key directly exposing public keys
Address Reuse: Approximately 20–50% of Bitcoin exists in addresses that have spent funds, revealing public keys
Mempool Attacks: Real-time attacks could extract public keys from unconfirmed transactions and compute private keys within Bitcoin's 10-minute confirmation window
Ethereum Exposure Analysis:
Account Model: Every address that has sent a transaction reveals its public key on-chain
Smart Contract Exposure: Multi-sig wallets, DeFi protocols, and governance systems create complex vulnerability chains
Cross-Chain Bridges: Multi-signature bridge implementations expose aggregated public keys across ecosystems
NIST Post-Quantum Cryptography Standards
The Standardization Landscape
After an 8-year global competition, NIST has standardized a portfolio of quantum-resistant algorithms. Crucially, recent cryptanalytic breaks (SIKE in 2022, Rainbow, GeMSS) demonstrate the danger of relying on single mathematical approaches, necessitating algorithmic diversity.
Algorithm Portfolio Strategy:
Primary Standards: ML-KEM, ML-DSA, SLH-DSA (FIPS 203–205, August 2024)
Secondary Standards: HQC selected March 2025, FALCON expected 2025
Diversity Requirement: Multiple mathematical foundations (lattices, hash functions, error-correcting codes) prevent catastrophic failure if one assumption breaks
Critical Algorithm Analysis for Blockchain
ML-DSA (CRYSTALS-Dilithium)
Primary Signature Candidate
Signature Size: 2,420–4,595 bytes vs. ECDSA's 64 bytes
Blockchain Impact: Bitcoin block capacity reduced to 400 transactions/block (95% reduction)
Advantages: Fast verification, deterministic signing, extensive cryptanalysis
FN-DSA (FALCON)
Compact Alternative
Signature Size: ~666 bytes for 128-bit security
Performance Trade-off: Complex implementation but smallest lattice signatures
Use Case: Constrained environments where signature size dominates
SLH-DSA (SPHINCS+)
Conservative Backup
Signature Size: 7,856–49,856 bytes impractical for most blockchain applications
Security Foundation: Relies only on hash functions, providing conservative security
Role: Emergency fallback if lattice assumptions break
Migration Architectures: The Hybrid Imperative
Given the performance catastrophe of pure PQC migration and the cryptanalytic risks of new algorithms, hybrid cryptography emerges as the only viable strategy.
Hybrid Implementation Framework
Phase 1 — Optional Hybrid (2026–2028):
Transactions carry both ECDSA and PQC signatures
Verification requires both to pass
Provides immediate quantum resistance for forward-looking applications
Bitcoin example: ECDSA (64 bytes) + ML-DSA-65 (3,293 bytes) = 3,357 bytes total
Phase 2 — Incentivized Adoption (2028–2030):
Reduced fees for hybrid transactions
Governance advantages for hybrid-signing validators
Education campaigns highlighting SNDL risks
Phase 3 — Mandatory Hybrid (2030–2032):
New addresses must use hybrid signatures
Legacy addresses cannot receive new funds
Multi-sig contracts require PQC components
Phase 4 — PQC Transition (2032+):
Gradual phase-out of classical component
Emergency override if PQC algorithm compromised
Crypto-Agility: Non-Negotiable Requirement
Recent cryptanalytic breaks demonstrate that algorithm flexibility is essential:
SIKE Break (2022): Broken in 1 hour on a laptop using mathematical structure
Rainbow Break: Multi-variate signature scheme compromised
GeMSS Break: Another multi-variate scheme showing vulnerabilities
Crypto-Agility Implementation:
Algorithm identifiers in transaction formats 0x01=ECDSA, 0x02=ML-DSA-65, etc.
Versioned address formats indicating required algorithms
Soft-fork mechanisms for adding new algorithms
Graceful degradation protocols for compromised algorithms
Blockchain-Specific Implementations
Bitcoin: BIP-360 and the Hard Fork Dilemma
Bitcoin faces the most challenging migration due to its conservative governance and emphasis on backward compatibility.
BIP-360 "Pay to Quantum Resistant Hash" Strategy:
SegWit v2 addresses (bc1r): Remove key-path spending entirely
Script-path only: Spending requires revealing pre-committed script and PQC signature
Attestation structure: hash(script || commitment) prevents arbitrary data inclusion
Backward compatibility: Older nodes see as anyone-can-spend security risk
The Governance Challenge:
Historical precedent shows Bitcoin's difficulty with purely defensive upgrades:
SegWit Activation (2017): Required 2+ years despite clear scaling benefits
Taproot Adoption (2021): Slow uptake despite privacy and efficiency improvements
PQC Migration: Offers no benefits until quantum computers exist, making consensus extraordinarily difficult
Proposed Bitcoin Timeline (Optimistic):
2026: BIP-360 soft fork activation
2026–2029: Dual-address period with migration incentives
2029: Legacy addresses cannot receive new funds
2031: Legacy UTXOs become unspendable extremely controversial
203X: Optional ZK proof recovery for lost coins
Ethereum: Account Abstraction Advantage
Ethereum's transition to account abstraction (EIP-7701) provides a more flexible migration path, as explicitly cited by Vitalik Buterin in The Splurge roadmap phase.
Account Abstraction Benefits:
Custom verification logic: Accounts define their own signature validation
Gradual migration: Users upgrade at their own pace
Multi-algorithm support: Can require multiple PQC signatures
Gas optimization: Batch verification reduces per-signature costs
Social recovery integration: Natural fit with quantum-resistant social recovery schemes
Ethereum-Specific Challenges:
Validator Security: PoS consensus relies on validator signatures vulnerable to quantum attacks
Smart Contract Exposure: Complex DeFi ecosystems create cascading vulnerabilities
Cross-Chain Bridges: Multi-sig implementations represent systemic risk
Permissioned Blockchains: Governance Advantage
Enterprise systems (Hyperledger, R3 Corda) benefit from coordinated governance but face unique challenges:
Testnet Performance Data:
Compensation Strategies:
Hardware scaling to maintain throughput
Signature aggregation for batch operations
Off-chain validation with on-chain commitments
Consortium-mandated upgrade timelines
Performance Impact: The Inescapable Catastrophe
Quantitative Analysis of PQC Impact
Bitcoin Block Capacity Analysis (1MB blocks):
Network-Wide Implications:
Fee Economics: 2–3x fee increases assuming constant demand
Full Node Requirements: 60–100x storage increase makes archival nodes impractical
Light Client Viability: SPV proofs become prohibitively large
Initial Block Download: Days to weeks longer for new nodes
Orphan Rate Risk: Larger blocks propagate slower, increasing chain reorganizations
The Block Size Dilemma
The performance catastrophe creates inevitable pressure to increase block sizes:
Bitcoin: Increasing from 1MB to 8MB would restore ECDSA-era capacity with ML-DSA-65
Ethereum: Gas limit increases would compensate but increase state growth
Governance Conflict: Block size debates Bitcoin's 2017 “Blocksize War” would re-emerge with quantum urgency
Decentralization Trade-off: Larger blocks favor centralized actors with better infrastructure
Migration Timelines: The Closing Window
Enterprise Migration Timelines (Campbell et al., 2025)
Small Enterprise
5–7 years baseline
3–4 optimistic, 8–10 pessimistic
Medium Enterprise
8–12 years baseline
5–6 optimistic, 12–15 pessimistic
Large Enterprise
12–15+ years baseline
8–10 optimistic, 15–20+ pessimistic
Blockchain Network Realities:
Bitcoin/Ethereum: 10–15 years realistic 5–7 optimistic likely unachievable
Permissioned Networks: 5–8 years with coordinated governance
New Blockchains: Immediate deployment possible (QRL, Quranium examples)
The Timeline Collision Crisis
Critical Convergence:
The Defensive Downgrade Paradox:
Unlike beneficial upgrades that offer immediate improvements, PQC migration:
- Imposes immediate severe costs throughput loss, fee increases
- Provides no tangible benefits until quantum computers exist
- May never benefit users if quantum computing progress stalls
- Requires extraordinary consensus for purely defensive change
Real-World Use Cases and Vulnerabilities
Central Bank Digital Currencies (CBDCs)
CBDCs represent the most urgent PQC deployment scenario due to:
National Security Implications: Quantum attacks could destabilize economies
Long Operational Lifespans: Must remain secure for 30–50+ years
Regulatory Mandates: EU Digital Euro explicitly considering PQC requirements
Privacy Catastrophe: Financial transaction history especially vulnerable to SNDL
Decentralized Finance (DeFi) Systemic Risk
DeFi's $100+ billion ecosystem faces cascading vulnerabilities:
Automated Market Makers: Price oracle signatures could be forged for profitable arbitrage
Lending Protocols: Unauthorized liquidations and collateral seizures
Governance Attacks: Forged votes to drain treasuries or pass malicious upgrades
Cross-Chain Bridges: $2+ billion bridge hacks in 2022 demonstrate existing vulnerabilities
Supply Chain and IoT Applications
Enterprise blockchain applications face unique challenges:
Long Product Lifecycles: Automotive and aerospace parts tracked for decades
Regulatory Compliance: Pharmaceutical tracking requires long-term integrity
IoT Constraints: Resource-constrained devices struggle with PQC performance
Interoperability Requirements: Multi-enterprise systems need coordinated migration
Active Research Frontiers
Post-Quantum Zero-Knowledge Proofs
ZK-proof systems enable privacy and scaling but face quantum challenges:
ZK-STARKs: Quantum-resistant through hash-based commitments but large proof sizes
Lattice-Based ZK-SNARKs: Combining FHE with ZK for compact quantum-resistant proofs
Proof Aggregation: Research into aggregating multiple PQC signatures into constant-size proofs
Hardware Acceleration
Performance catastrophe necessitates specialized hardware:
FPGA Implementations: NTT operations accelerated 10–100x
ASIC Development: Dedicated lattice arithmetic units
HSM Integration: Hardware security modules with PQC support (Infineon, Wibu-Systems)
Mobile Optimization: Resource-constrained implementations for wallet applications
Threshold Cryptography and Consensus
BFT consensus mechanisms require PQC adaptations:
Threshold Signatures: Distributed key generation for validator security
Aggregate Signatures: Constant-size multi-signatures for PoS systems
Leader Election: Quantum-resistant VRF Verifiable Random Function implementations
Slashing Proofs: Alternative accountability mechanisms for signature-less systems
Conclusion and Recommendations
The Existential Reality
The post-quantum migration of blockchain represents more than a technical challenge — it is an existential crisis requiring immediate, coordinated action. The collision between quantum capability timelines and migration requirements creates a closing window that demands unprecedented cooperation across the blockchain ecosystem.
For Blockchain Projects (2026–2027):
Cryptographic Inventory: Document all quantum-vulnerable components across protocol layers
Testnet Deployment: Implement PQC algorithms on test networks for performance benchmarking
Community Education: Launch comprehensive education campaigns highlighting SNDL risks
Governance Proposals: Begin consensus-building for migration timelines and mechanisms
For Enterprises and Developers (2026–2028):
Crypto-Agility Implementation: Build algorithm flexibility into all new systems
Hybrid Deployment: Implement optional hybrid signatures in wallets and services
Key Management Updates: Revise key generation, storage, and rotation policies for PQC
Interoperability Testing: Verify cross-chain and cross-platform compatibility
For Researchers and Standards Bodies (2026–2030):
Performance Optimization: Focus on signature aggregation and compression techniques
Algorithm Diversity: Continue development of alternative mathematical approaches
Hardware Acceleration: Develop efficient implementations for resource-constrained environments
Migration Tooling: Create automated tools for address migration and key rotation
The Inevitable Trade-offs
Accepting several uncomfortable realities is essential for realistic migration planning:
- Performance Degradation is Unavoidable: 50–70% throughput reduction must be accepted or compensated via block size increases
- Hybrid Approach is Essential: No single algorithm can be trusted; defense-in-depth requires multiple mathematical approaches
- Governance Will Be Contentious: Defensive downgrades face extraordinary consensus challenges in decentralized systems
- Some Assets May Be Lost: Unmigrated funds in vulnerable addresses represent unavoidable risk
- Timeline Compression is Necessary: 15-year migrations must be compressed into 5–7 year windows
Final Assessment:
The quantum threat to blockchain is no longer speculative — it is a predictable engineering challenge with known parameters and timelines. The migration represents the largest cryptographic transition in history, requiring coordination across thousands of independent projects, millions of users, and trillions in assets.
Success requires acknowledging the performance catastrophe, embracing hybrid cryptography as an essential interim solution, and beginning immediate migration efforts despite the defensive nature of the upgrade. The alternative — waiting until quantum capabilities are demonstrated — risks catastrophic failure of the entire blockchain ecosystem.
The window for orderly migration is closing. The time for action is now.
Case Studies
Empowering Digital
Evolution
Blogs
Empowering Digital
Evolution
BitViraj Technologies - Your Gateway to
Tomorrow's Innovations
Embark on a DigitalJourney


The next-generation digital technology company Bitviraj has the potential to empower and reinvent business in the current fast-paced market.
Our Service
- Website Development
- Application Development
- Blockchain Development
- Gaming and Metaverse